Surveillance Will Soon Be the Lesser of Your Worries
F-Secure Weblog Ref:- http://www.f-secure.com/weblog/archives/00002578.html
According to what has happened, the NSA Prism Programme is base on facts.
I don't think Snowden is lying.
It seems that companies like Apple, Microsoft, Google, Yahoo and others are involve.
If you were to look at the NSA wikis, it all written there.
http://en.wikipedia.org/wiki/National_Security_Agency
It can even stated in the NSA Wikis,
see the excerpt:-
Data mining[edit]
NSA is reported to use its computing capability to analyze "transactional" data that it regularly acquires from other government agencies, which gather it under their own jurisdictional authorities. As part of this effort, NSA now monitors huge volumes of records of domestic emails and Internet searches as well as bank transfers, credit-card transactions and travel and telephone records, according to current and former intelligence officials interviewed by The Wall Street Journal.[81]
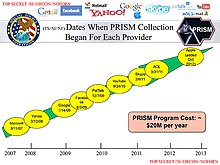
The NSA began the PRISM electronic surveillance and data mining program in 2007.[82][83]PRISM gathers communications data on foreign targets and United States citizens from nine major U.S. internet-based communication service providers: Microsoft, Yahoo, Google, Facebook, PalTalk, AOL, Skype, YouTube and Apple. Data gathered include email, video and voice chat, videos, photos, voice-over-IP chats such as Skype, and file transfers. Another program, Boundless Informant, employs big data databases, cloud computing technology, and Free and Open Source Software (FOSS) to analyze data collected worldwide by the NSA, including that gathered by way of the PRISM program.[84][citation needed]
The Real Time Regional Gateway was a data collection program introduced in 2005 in Iraq by NSA during the Iraq War. It consisted of gathering all Iraqi electronic communication, storing it, then searching and otherwise analyzing it. It was effective in providing information about Iraqi insurgents who had eluded less comprehensive techniques.[85] Glenn Greenwald of The Guardian believes that the "collect it all" strategy introduced by NSA director Alexander shows that "the NSA's goal is to collect, monitor and store every telephone and internet communication" worldwide.[86
And you can even find infos here...
http://en.wikipedia.org/wiki/PRISM_(surveillance_program)
Companies that suspecting inviolve in the Prism programme.
Please read the excerpts here:-
Initial public statements
Corporate executives of several companies identified in the leaked documents told The Guardian that they had no knowledge of the PRISM program in particular and also denied making information available to the government on the scale alleged by news reports.[2][89]Statements of several of the companies named in the leaked documents were reported by TechCrunch and The Washington Post as follows:[90][91]

- Microsoft: "We provide customer data only when we receive a legally binding order orsubpoena to do so, and never on a voluntary basis. In addition we only ever comply with orders for requests about specific accounts or identifiers. If the government has a broader voluntary national security program to gather customer data we don't participate in it."[90][93]
- Yahoo!: "Yahoo! takes users' privacy very seriously. We do not provide the government with direct access to our servers, systems, or network."[90] "Of the hundreds of millions of users we serve, an infinitesimal percentage will ever be the subject of a government data collection directive."[91]
- Facebook: "We do not provide any government organization with direct access to Facebook servers. When Facebook is asked for data or information about specific individuals, we carefully scrutinize any such request for compliance with all applicable laws, and provide information only to the extent required by law."[90]
- Google: "Google cares deeply about the security of our users' data. We disclose user data to government in accordance with the law, and we review all such requests carefully. From time to time, people allege that we have created a government ‘back door' into our systems, but Google does not have a backdoor for the government to access private user data."[90] "[A]ny suggestion that Google is disclosing information about our users' Internet activity on such a scale is completely false."[91]
- Apple: "We have never heard of PRISM. We do not provide any government agency with direct access to our servers, and any government agency requesting customer data must get a court order."[94]
- Dropbox: "We've seen reports that Dropbox might be asked to participate in a government program called PRISM. We are not part of any such program and remain committed to protecting our users' privacy."[90]
Remember the DigiNotar Case???
Nothing new!
Bruce Sheiner did indicate of possible Backdoors on Microsoft products.
http://www.wired.com/politics/security/commentary/securitymatters/2007/11/securitymatters_1115
Remember Bruce Scheiner did indicate about NSAKEY on Windows.
http://en.wikipedia.org/wiki/NSAKEY
The NSAKEY got nothing to do with 9/11. These things already happen way before 9/11!!!
Backdoor???
It's been there all the time.
It happen to all OSes!
Regardless what OSes you are using, it happen to a Apple MAC OS X, Linux, BSD, Microsoft.
It''s already been there!
Selinux done by whom? Trusted BSD done by whom??
Apple is infact runs under BSD. So I believe it's still there.
All are done by the NSA.
It's a NSA technologies.
Well, I have nothing against them.
I still think that these things are REAL!
Even there is a FBI backdoor!!!!
Believe it or not.
http://www.wnd.com/2013/06/now-fbi-wants-back-door-to-all-software/
It's their National Security Interest!
They gathering for intelligence. Information gathering to individuals.
They are the code breakers!
They are expert and well verse in Communications (Project Echelon) and Computers technologies.
They have cryptographers and mathematicians.
They can break codes and passwords very easily because they runs SuperComputers at their end.
Since the early ENIAC computers!
http://www.acsa.net/a_computer_saved_the_world.htm
Of course!!!
Everyone got freak out by it.
No matter what, the backdoor will always be there.
It's their National Security Interest!
Every Computer Security Experts, Cryptographers and Mathematicians knows about these subjects!
Remember they are run by "Enlightened" groupies!
I'm stunned that Snowden was a Certified Ethical Hacker! Maybe a CISSP!
http://www.newser.com/story/170531/snowden-was-certified-ethical-hacker-resume.html
I come to realise that all of them are computer security experts!
Most of them are trained in these fields.
Sounds like the movie "Enemy of the States"
http://en.wikipedia.org/wiki/Enemy_of_the_State_(film)
Comments
-
I am worried about the 1.5 BILLION ROUNDS OF AMMUNITION THE DEPARTMENT OF HOMELAND SECURITY PURCHASED NOT MY COMPUTER! If I surf for porn I do not care who knows about it because I do not believe it is a matter of national security but that is enough Ammo to invade South Korea! Except this is the Department of HOMELAND meaning IN the UNITED STATES. Just how much Fire power do they think the terrorists have and how many terrorists do they think they have a million in the US? Either that or they are the worst shots in the history of mankind or they forsee a breakdown of civilization or something is coming and I do not understand why anyone would do something like that Rusli. When we were already fighting two wars. What war is next one against Veterans who are so messed up they can not sleep at night because they did all they asked them too and now have no normal life left?