New proof-of-concept malware demonstrates virus for OS X - Clapzok.A
New proof-of-concept malware demonstrates virus for OS X
Clapzok.A is a new malware approach that, with current (albeit limited) loopholes in OS X, can spread among binary files when executed, making it one of the first-known, true computer viruses for OS X.
Security researchers have found a proof-of-concept attack that appears to be the first true viral malware approach for compromising OS X.
The malware is called "Clampzok.A" and is a cross-platform malware package that alters the binary files on an affected system so when executed, the binary will infect neighboring binary files.
The malware is written in assembly code, and was originally released in 2006 for Windows and Linux systems, but was recently updated to affect 32-bit Mach-O binary files in OS X machines.
Unlike Trojan horses, spyware, and adware that hide in one location on the system and persistently run to steal information or otherwise be a nuisance, viral malware attempts to spread itself around the system. Of these, a form known as a worm will try to replicate itself, but does not infect otherwise healthy files. The classic virus, by contrast, will inject itself into the compiled code of an executable or into the structure of a file, modifying it significantly so that when the file is read, the virus is executed and further injects itself around the system, wreaking havoc on the system's ability to function.
This latest malware shows promise to do just that.
When infected, the virus will modify the __PAGEZERO segment of a healthy binary so it holds the virus code. With other modifications to this segment the virus enables both read and execution ability on this code. Next, the virus alters the command "LC_UNIXTHREAD" in the binary so it points to the location of the virus instead of the desired execution point of the binary file.
When the binary is then executed, the virus code will run and search for additional 32-bit binary files in the same environment as the infected one, and attempt the injection on them. The malware tries to target the BSD tools and other programs stored in the /bin and /usr/bin directories on OS X systems.
In this manner, if one executes simple terminal commands on an affected system, then other terminal tools could get infected.
This development marks one of the first such viral attacks that can affect the OS X platform; however, it does have its limitations, both in current function and in its ability to hide. For one, the attack only works on 32-bit Mach-O binary files. While there are still plenty of 32-bit programs for OS X, recent versions are migrating to 64-bit code.
In addition, if a system is infected with malware that uses this mode of attack, then it will be easily detectable since a scanner simply needs to check for the read and execute ability on the __PAGEZERO segment of the binary. If this exists, then the binary has been compromised and can be easily quarantined or otherwise flagged. Furthermore, this attack will break code-signed programs, so any that have a valid signature (i.e.those from the Mac App Store) will no longer work if infected.
Overall, while this development does outline a true viral attack on OS X, it is just a proof of concept effort, meaning it is not used in any known malware on OS X. Additionally, it is so far quite limited in scope, and easy to detect. Does this mean you need to lock down your system? Not at all. However, it may be wise to simply be mindful that malware efforts are ongoing for the Mac platform, and among the various Trojan horse attempts, even viral breakthroughs are occurring.
Comments
-
URL:- http://www.intego.com/mac-security-blog/clapzok-a-multi-platform-virus/
Multi-Platform Proof of Concept Virus Clapzok.A Examined
Posted on June 4th, 2013 by Peter James
A multi-platform virus, named Multi/Clapzok.A, have been released by researcher JPanic. It is written in Assembly, and targets Windows, Linux and OS X 32-bit executables.
This proof of concept is an update of JPanic’s Capzloq Tekniq(2006), that targets Windows and Linux operating systems. The OS X infection process is similar to the concept Roy G Biv exposed with MachoMan (2006) on VX Heavens.
Peter Ferrie, Principal Anti-virus Researcher at Microsoft Corporation, has published an analysis in the Virus Bulletin issue of June 2013. While this content is only available to subscribers, well known reverser Fractal Guru also published a technical analysis of the OS X infection on his blog.
In short, when the virus is executed, it looks for other 32-bit executables (either Windows, Linux or OS X native and FAT binaries) to replicate itself.
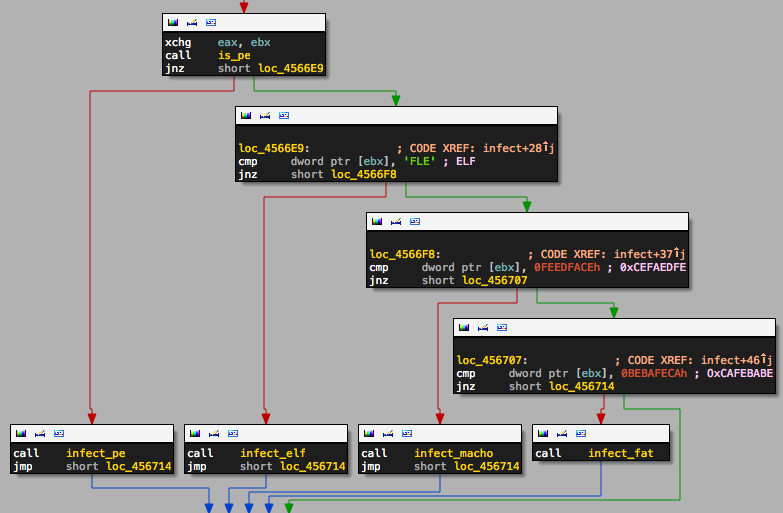
On OS X, it modifies the __PAGEZERO load command to store its code, then changes the entry point in LC_UNIXTHREAD to trigger its execution. It then restores the original entry point in memory, so the infected program can run normally.
It does not infect 64-bit executables (shellcode is 32-bit) or programs built with the latest Developer Tools, where GCC’s LC_UNIXTHREAD has been replaced by LC_MAIN in Clang. Also, fat binaries that contain both i386 and x86_64 architectures, running on a 64-bit machine, won’t execute the virus payload. Finally, a code-signed binary would detect the modification.
Despite the significant limitations, this academics research is interesting as it exposes simple caveats Apple hasn’t patch since 2006.
JPanic has not published his source code yet, and our malware researchers have not spotted any malicious use of his work.
Intego VirusBarrier with latest Virus Definitions detect Multi/Clapzok.A and similar __PAGEZERO load command abuses.
This entry was posted in Security News and tagged clapzok, multi,poc. Bookmark the permalink.
